I don’t dislike that art style in general, but to my mind it seems like a poor fit for a Dragon Age game. I guess they’re pivotinf strongly away from the series dark and gritty roots, which is unfortunate because I think that was one of its strong points.
- 0 Posts
- 97 Comments
- CountVon@sh.itjust.workstoGames@lemmy.world•Dragon Age: The Veilguard | Review ThreadEnglish91·6 days ago
- CountVon@sh.itjust.workstoGames@lemmy.world•Dragon Age: The Veilguard | Review ThreadEnglish202·6 days ago
Watching Skill Up’s review now, and oof. That art style… that writing. Don’t know who they made this game for, but it’s definitely not me.
- CountVon@sh.itjust.workstoTechnology@lemmy.world•It’s Time to Stop Taking Sam Altman at His WordEnglish191·30 days ago
Oh I’m streets ahead, I never took him at his word in the first place.
- CountVon@sh.itjust.workstoTechnology@lemmy.world•OpenAI is reportedly going all-in as a for-profit companyEnglish31·2 months ago
OpenAI on that enshittification speedrun any% no-glitch!
Honestly though, they’re skipping right past the “be good to users to get them to lock in” step. They can’t even use the platform capitalism playbook because it costs too much to run AI platforms. Shit is egregiously expensive and doesn’t deliver sufficient return to justify the cost. At this point I’m ~80% certain that AI is going to be a dead tech fad by the end of this decade because the economics just don’t work now that the free money era has ended.
- CountVon@sh.itjust.workstoFirefox@lemmy.ml•Why doesn't Firefox implement Private State Tokens?English2·2 months ago
Tl;Dr the protocol requires there to be trusted token providers that issue the tokens. Who do you suppose are the trusted providers in the Google and Apple implementations? Google and Apple respectively, of course. Maybe eventually there would be some other large incumbents that these implementers choose to bless with token granting right. By its nature the protocol centralizes power on the web, which would disadvantage startups and smaller players.
- CountVon@sh.itjust.workstoFirefox@lemmy.ml•Why doesn't Firefox implement Private State Tokens?English51·2 months ago
Private State Tokens are Google’s implementation of the IETF Privacy Pass protocol. Apple has another implementation of the same protocol named Private Access Tokens. Mozilla has taken a negative position against this protocol in its current form, and its existing implementations in their current forms. See here for their blog post on the subject, and here for their more in-depth analysis.
- CountVon@sh.itjust.workstoPiracy: ꜱᴀɪʟ ᴛʜᴇ ʜɪɢʜ ꜱᴇᴀꜱ@lemmy.dbzer0.com•Alternative/manual way to fix cloudflare-locked trackers on ProwlarrEnglish141·2 months ago
I think you’re referring to FlareSolverr. If so, I’m not aware of a direct replacement.
Main issue is it’s heavy on resources (I have an rpi4b)
FlareSolverr does add some memory overhead, but otherwise it’s fairly lightweight. On my system FlareSolverr has been up for 8 days and is using ~300MB:
NAME CPU % MEM USAGE flaresolverr 0.01% 310.3MiBNote that any CPU usage introduced by FlareSolverr is unavoidable because that’s how CloudFlare protection works. CloudFlare creates a workload in the client browser that should be trivial if you’re making a single request, but brings your system to a crawl if you’re trying to send many requests, e.g. DDOSing or scraping. You need to execute that browser-based work somewhere to get past those CloudFlare checks.
If hosting the FlareSolverr container on your rpi4b would put it under memory or CPU pressure, you could run the docker container on a different system. When setting up Flaresolverr in Prowlarr you create an indexer proxy with a tag. Any indexer with that tag sends their requests through the proxy instead of sending them directly to the tracker site. When Flaresolverr is running in a local Docker container the address for the proxy is localhost, e.g.:
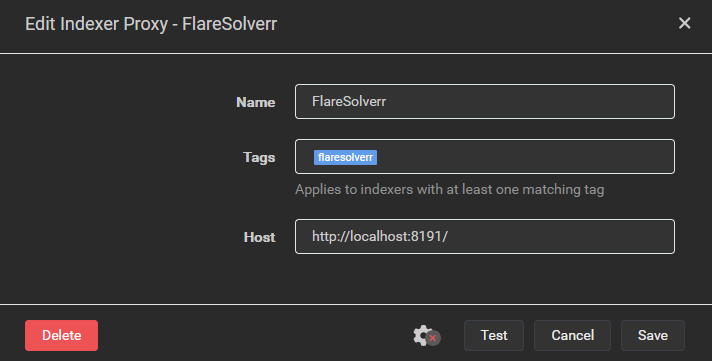
If you run Flaresolverr’s Docker container on another system that’s accessible to your rpi4b, you could create an indexer proxy whose Host is “http://<other_system_IP>:8191”. Keep security in mind when doing this, if you’ve got a VPN connection on your rpi4b with split tunneling enabled (i.e. connections to local network resources are allowed when the tunnel is up) then this setup would allow requests to these indexers to escape the VPN tunnel.
On a side note, I’d strongly recommend trying out a Docker-based setup. Aside from Flaresolverr, I ran my servarr setup without containers for years and that was fine, but moving over to Docker made the configuration a lot easier. Before Docker I had a complex set of firewall rules to allow traffic to my local network and my VPN server, but drop any other traffic that wasn’t using the VPN tunnel. All the firewall complexity has now been replaced with a gluetun container, which is much easier to manage and probably more secure. You don’t have to switch to Docker-based all in go, you can run hybrid if need be.
If you really don’t want to use Docker then you could attempt to install from source on the rpi4b. Be advised that you’re absolutely going offroad if you do this as it’s not officially supported by the FlareSolverr devs. It requires install an ARM-based Chromium browser, then setting some environment variables so that FlareSolverr uses that browser instead of trying to download its own. Exact steps are documented in this GitHub comment. I haven’t tested these steps, so YMMV. Honestly, I think this is a bad idea because the full browser will almost certainly require more memory. The browser included in the FlareSolverr container is stripped down to the bare minimum required to pass the CloudFlare checks.
If you’re just strongly opposed to Docker for whatever reason then I think your best bet would be to combine the two approaches above. Host the FlareSolverr proxy on an x86-based system so you can install from source using the officially supported steps.
- CountVon@sh.itjust.workstoLemmy Shitpost@lemmy.world•I wonder what they smell like.English71·3 months ago
They smell like plastic, metal, complex hydrocarbons, and death.
- CountVon@sh.itjust.workstoLinux@lemmy.ml•Edit: it's CentOS 7 (original: CentOS 3 on a self checkout?!?)English39·3 months ago
It’s likely CentOS 7.9, which was released in Nov. 2020 and shipped with kernel version 3.10.0-1160. It’s not completely ridiculous for a one year old POS systems to have a four year old OS. Design for those systems probably started a few years ago, when CentOS 7.9 was relatively recent. For an embedded system the bias would have been toward an established and mature OS, and CentOS 8.x was likely considered “too new” at the time they were speccing these systems. Remotely upgrading between major releases would not be advisable in an embedded system. The RHEL/CentOS in-place upgrade story is… not great. There was zero support for in-place upgrade until RHEL/CentOS 7, and it’s still considered “at your own risk” (source).
- CountVon@sh.itjust.workstoTechnology@lemmy.world•Unreal Engine supervisor at ModelFarm blasts 50% failure rate with Intel chips — company switching to AMD's Ryzen 9 9950X, praises single-threaded performanceEnglish28·3 months ago
Anything that pushes the CPUs significantly can cause instability in affected parts. I think there are at least two separate issues Intel is facing:
- Voltage irregularities causing instability. These could potentially be fixed by the microcode update Intel will be shipping in mid-August.
- Oxidation of CPU vias. This issue cannot be fixed by any update, any affected part has corrosion inside the CPU die and only replacement would resolve the issue.
Intel’s messaging around this problem has been very slanted towards talking as little as possible about the oxidation issue. Their initial Intel community post was very carefully worded to make it sound like voltage irregularity was the root cause, but careful reading of their statement reveals that it could be interpreted as only saying that instability is a root cause. They buried the admission that there is an oxidation issue in a Reddit comment, of all things. All they’ve said about oxidation is that the issue was resolved at the chip fab some time in 2023, and they’ve claimed it only affected 13th gen parts. There’s no word on which parts number, date ranges, processor code ranges etc. are affected. It seems pretty clear that they wanted the press talking about the microcode update and not the chips that will have the be RMA’d.
- CountVon@sh.itjust.workstoGames@lemmy.world•Are there any good casual/low-stress mobile games that aren't filled with microtransactions?English5·4 months ago
I’m not sure it fits 100% with what you’re looking for, but I’ll take chance and recommend Slice & Dice (Google Play, Apple App Store). Free demo, no ads, single in-app purchase to unlock the full version. This game is easily the best value-for-dollar mobile game I’ve ever purchased.
Oh for sure, those are a communal resource.
- CountVon@sh.itjust.workstoAsklemmy@lemmy.ml•Why do I puke more than once when I've been drunk?English15·5 months ago
Because the toxins your body is reacting to are already in your bloodstream. It’ll take time for those to get metabolized by your liver, and how much or little you vomit won’t change how much work your liver has to do.
One of my grandfathers worked for a telephone company before he passed. That man was an absolute pack rat, he wouldn’t throw anything away. So naturally he had boxes and boxes of punch cards in this basement. I guess they were being thrown out when his employer upgraded to machines that didn’t need punch cards, so he snagged those to use as note paper. I will say, they were great for taking notes. Nice sturdy card stock, and the perfect dimensions for making a shopping list or the like.
He was a raging alcoholic who hid his illness from the medical professionals who examined him as part of his Super Size Me “experiment.” A lifetime of booze did way more damage than 30 days of McDs possibly could.
- CountVon@sh.itjust.workstoaww@lemmy.world•Here's my dude. I have no idea what he is.English182·6 months ago
I’d definitely agree that it’s a Pit Bull cross with a shepherd of some kind. The shape of the face definitely suggests Pit Bull to me, but I get more of a Belgian Malinois vibe from those ears:

Could explain why two hours at a dog park didn’t crush his energy levels, Malinois are renowned and/or notorious for their exercise needs.
That was actually the rest of the comic:
- CountVon@sh.itjust.workstomemes@lemmy.world•Gimme some other phrases that work this wayEnglish7·6 months ago
Hey, leave Laura Palmer out of this, she’s been through enough already.
Yeah, I don’t get it either. What I’ve seen doesn’t look anywhere close to an 8+ out of ten rating. Will be interesting to see the player ratings on this one…